Description:
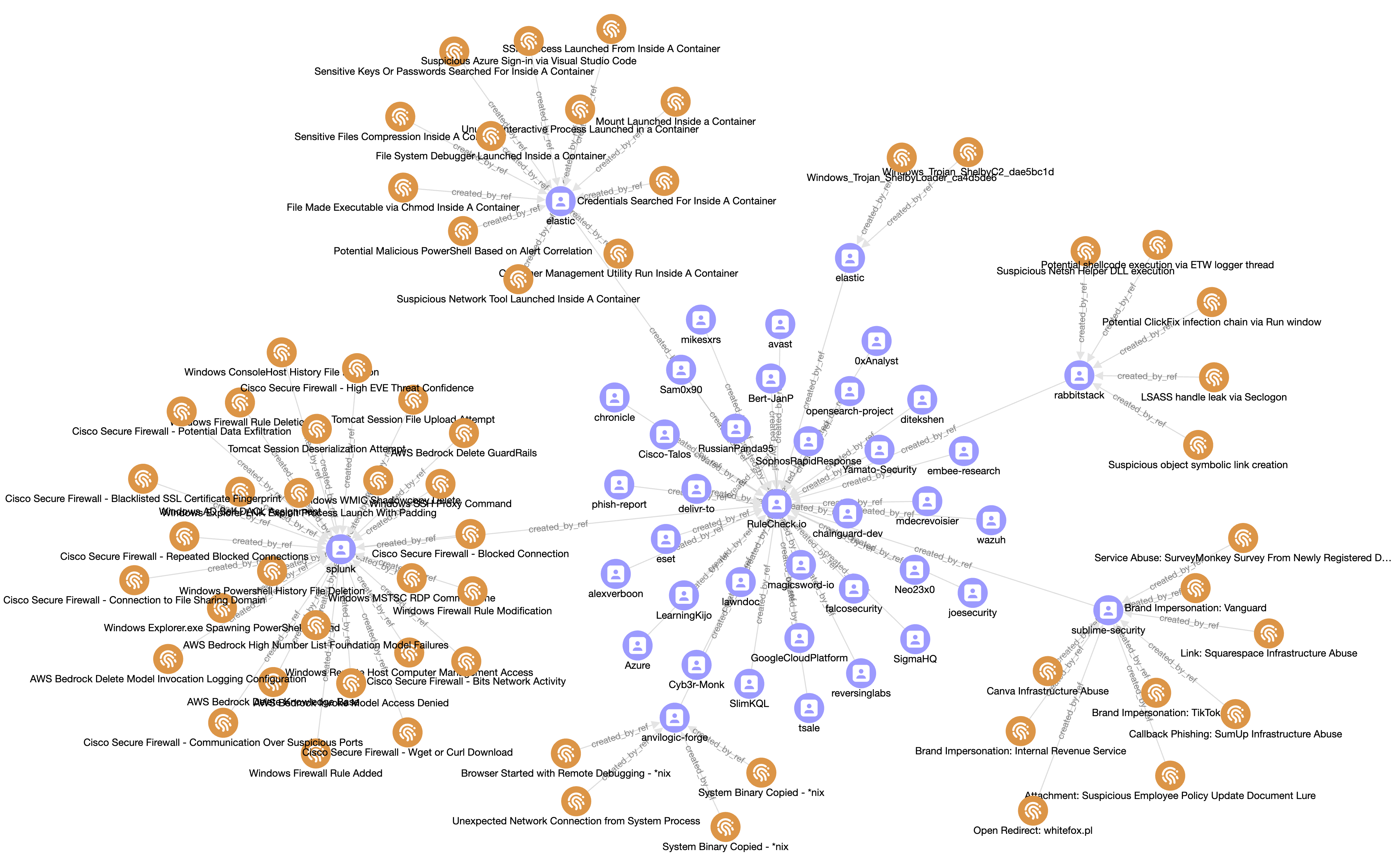
The feed offers a continuous stream of newly published detection rules, sourced from 50+ public GitHub repositories. It is designed for individual researchers, students, or security teams on a limited budget looking to track emerging detection trends and gain early visibility into new detection methods.
Use cases:
- Early threat awareness - observe new detection patterns that may correspond to novel attack techniques or malware variants.
- Research & learning - the feed is an excellent resource for understanding how different organizations and individuals approach threat detection.
- Idea generation - spark inspiration for developing your own custom detection rules by seeing what the industry does.
Rules:
anvilogic: 75elastic-edr: 288elastic-siem: 296fibratus: 14kql: 172osquery: 6sentinel: 1sigma: 294splunk: 283sublime: 3sublime-security: 234yara: 101
Entities:
Identity: 52 Indicator: 1767
MISP feed:
STIX/TAXII feed:
Content preview:
Latest 10 entities:
STIX2 bundle ↗This rule detects inbound emails where the sender and recipient are the same, a condition often used to bypass sender reputation checks. It specifically looks for messages with a PDF attachment that contains only the string 'VIEW PDF'. The email body must also start with a generic phrase like 'Please see attached', which is common in low-effort phishing campaigns. Relevant MITRE ATT&CK tactics: TA0001 Relevant MITRE ATT&CK techniques: T1566.001
name: "Attachment: Self-sender PDF with minimal content and view prompt" description: "Detects messages where the sender and recipient are the same address with a PDF attachment containing only 'VIEW PDF' text and a standardized body message requesting to view the attachment." type: "rule" severity: "medium" source: | type.inbound // self sender and length(recipients.to) == 1 and ( sender.email.email == recipients.to[0].email.email or recipients.to[0].email.domain.valid == false ) and strings.starts_with(body.current_thread.text, 'Please see attached') and any(filter(attachments, .file_type == 'pdf'), any(file.explode(.), .scan.strings.strings[0] == 'VIEW PDF' and length(.scan.strings.strings) == 1 ) ) attack_types: - "Credential Phishing" - "Malware/Ransomware" tactics_and_techniques: - "PDF" - "Social engineering" - "Evasion" detection_methods: - "Content analysis" - "File analysis" - "Sender anal...malicious-activity credential-access TA0001 T1566.001 MIT License
This KQL query detects suspicious processes spawned by "gup.exe", a component of Notepad++, which could indicate the Chrysalis backdoor activity. The query leverages an external data source of legitimate Notepad++ file hashes to exclude known-good instances, reducing false positives. It further filters out common processes such as explorer.exe and msedge.exe to focus on anomalous behavior potentially related to the supply chain compromise. Relevant MITRE ATT&CK tactics: TA0002, TA0005 Relevant MITRE ATT&CK techniques: T1195.002, T1574.002
//Credit: https://medium.com/capturedsignal/notepad-security-incident-threat-hunting-using-kql-and-defender-for-endpoint-logs-dd83b984fcc6 //Credit to: Bartosz Turek and Florian Roth let NotepadHashes = externaldata( version_tag: string, release_title: string, release_date: datetime, prerelease: bool, release_url: string, hash_algorithm: string, hash_value: string, inferred_asset_name: string, source_location: string, checksum_asset_name: string, checksum_asset_url: string ) [h@'https://raw.githubusercontent.com/Neo23x0/notepad-plus-plus-hashes/refs/heads/main/notepadpp_release_hashes.csv'] with(format = "csv", ignoreFirstRecord = true) | distinct hash_value; DeviceProcessEvents | where TimeGenerated > todatetime('2025-06-01T00:00:00.00Z') // "The incident began from June 2025" | where InitiatingProcessCommandLine startswith '"gup.exe"' | where FolderPath <> "C:\\Windows\\explorer.exe" | where FolderPath <> "C:\\Program Files (x86)\\Microsoft\\Edge\\Application\\msedge.exe" | where not...malicious-activity endpoint-security TA0002 TA0005 T1195.002 T1574.002 MIT License
This KQL query hunts for activity related to the Chrysalis backdoor by identifying processes spawned by "gup.exe", a known indicator of a compromised Notepad++ updater. The query filters out legitimate processes like explorer.exe and msedge.exe, then correlates the SHA256 hash of the suspicious spawned binaries with subsequent network events they initiate. This links the initial execution from the backdoor to potential command-and-control or data exfiltration activities. Relevant MITRE ATT&CK tactics: TA0002, TA0011 Relevant MITRE ATT&CK techniques: T1204, T1071
//Credit: https://medium.com/capturedsignal/notepad-security-incident-threat-hunting-using-kql-and-defender-for-endpoint-logs-dd83b984fcc6 //Credit to: Bartosz Turek DeviceProcessEvents | where TimeGenerated > todatetime('2025-06-01T00:00:00.00Z') // "The incident began from June 2025" | where InitiatingProcessCommandLine startswith '"gup.exe"' | project-reorder TimeGenerated, DeviceName, ActionType, FileName, FolderPath, ProcessCommandLine, SHA1, SHA256, MD5 | where FolderPath <> "C:\\Windows\\explorer.exe" | where FolderPath <> "C:\\Program Files (x86)\\Microsoft\\Edge\\Application\\msedge.exe" | distinct SHA256 | join (DeviceNetworkEvents | where TimeGenerated > todatetime('2025-06-01T00:00:00.00Z')) on $left.SHA256 == $right.InitiatingProcessSHA256malicious-activity command-and-control endpoint-security TA0002 TA0011 T1204 T1071 MIT License
This KQL query detects the presence of the Chrysalis Backdoor by searching Microsoft Defender's DeviceFileEvents table. The detection is based on a list of known malicious file hashes (SHA256) and filenames associated with the backdoor, which was used by the Lotus Blossom group in a supply chain attack targeting Notepad++. The query looks back over a 90-day period for file creation events matching these specific indicators of compromise. Relevant MITRE ATT&CK tactics: TA0002, TA0003 Relevant MITRE ATT&CK techniques: T1195.002, T1574.002
// Reference: https://www.rapid7.com/blog/post/tr-chrysalis-backdoor-dive-into-lotus-blossoms-toolkit/ let FileHashes = dynamic(["a511be5164dc1122fb5a7daa3eef9467e43d8458425b15a640235796006590c9", "8ea8b83645fba6e23d48075a0d3fc73ad2ba515b4536710cda4f1f232718f53e","2da00de67720f5f13b17e9d985fe70f10f153da60c9ab1086fe58f069a156924","77bfea78def679aa1117f569a35e8fd1542df21f7e00e27f192c907e61d63a2e","3bdc4c0637591533f1d4198a72a33426c01f69bd2e15ceee547866f65e26b7ad","9276594e73cda1c69b7d265b3f08dc8fa84bf2d6599086b9acc0bb3745146600", "f4d829739f2d6ba7e3ede83dad428a0ced1a703ec582fc73a4eee3df3704629a","4a52570eeaf9d27722377865df312e295a7a23c3b6eb991944c2ecd707cc9906","831e1ea13a1bd405f5bda2b9d8f2265f7b1db6c668dd2165ccc8a9c4c15ea7dd","0a9b8df968df41920b6ff07785cbfebe8bda29e6b512c94a3b2a83d10014d2fd", "4c2ea8193f4a5db63b897a2d3ce127cc5d89687f380b97a1d91e0c8db542e4f8","e7cd605568c38bd6e0aba31045e1633205d0598c607a855e2e1bca4cca1c6eda","078a9e5c6c787e5532a7e728720cbafee9021bfec4a30e3c2be110748d7c43c...malicious-activity endpoint-security TA0002 TA0003 T1195.002 T1574.002 MIT License
The following analytic detects instances of Chromium-based browser processes on Windows launched with extensions explicitly disabled via command-line arguments. Disabling extensions can be used by automation frameworks, testing tools, or headless browser activity, but may also indicate defense evasion or abuse of browser functionality by malicious scripts or malware. This behavior reduces browser visibility and bypasses user-installed security extensions, making it relevant for detecting non-interactive execution, suspicious automation, or living-off-the-land techniques. Analysts should validate execution context, parent process, and command-line parameters to determine legitimacy. Relevant MITRE ATT&CK tactics: TA0005 Relevant MITRE ATT&CK techniques: T1497, T1562.007
name: Windows Chromium Process with Disabled Extensions id: ce245717-779b-483b-bc52-fc7a94729973 version: 1 date: '2026-01-23' author: Teoderick Contreras, Splunk status: production type: Anomaly description: The following analytic detects instances of Chromium-based browser processes on Windows launched with extensions explicitly disabled via command-line arguments. Disabling extensions can be used by automation frameworks, testing tools, or headless browser activity, but may also indicate defense evasion or abuse of browser functionality by malicious scripts or malware. This behavior reduces browser visibility and bypasses user-installed security extensions, making it relevant for detecting non-interactive execution, suspicious automation, or living-off-the-land techniques. Analysts should validate execution context, parent process, and command-line parameters to determine legitimacy. data_source: - Sysmon EventID 1 - Windows Event Log Security 4688 - CrowdStrike ProcessRollup2...defense-evasion endpoint-security TA0005 T1497 T1562.007 Apache License 2.0
This rule detects the execution of Chromium-based browsers (Chrome, Brave, Opera, Vivaldi, Edge) on Windows systems with command-line arguments that disable logging, such as "--disable-logging". While these flags can be used for legitimate debugging or testing, they are also employed by malware to evade monitoring and analysis. The detection logic identifies processes like "Chrome.exe" or "msedge.exe" whose command line contains the string "--disable-logging", indicating a potential attempt to hide malicious activity. Relevant MITRE ATT&CK tactics: TA0005 Relevant MITRE ATT&CK techniques: T1497, T1562, T1562.001
name: Windows Chromium Process Launched with Logging Disabled id: d31de944-4e61-468f-9154-e50690f0e99e version: 1 date: '2026-01-23' author: Teoderick Contreras, Splunk status: production type: Anomaly description: | The following analytic detects instances of Chromium-based browser processes on Windows launched with logging disabled via command-line arguments such as --disable-logging and --disable-logging-redirect. The --disable-logging flag forces browser logging to be disabled, while --disable-logging-redirect disables log redirection and is commonly used for testing or debugging scenarios. Logging is enabled by default in Chromium debug builds, making these flags more likely to appear in debug or development environments. While these options may be legitimately used by automation frameworks, debugging workflows, or isolated testing environments, they are also leveraged by malware and malicious scripts to evade security monitoring. Analysts should review the parent proces...defense-evasion endpoint-security TA0005 T1497 T1562 T1562.001 Apache License 2.0
This detection rule identifies instances where a Chromium-based browser process on Windows is launched with the `--disable-popup-blocking` command-line flag. This action bypasses the browser's native pop-up protection, enabling automatic execution of pop-ups or redirects without user consent. Although this can be used for legitimate testing, adversaries may leverage it to execute web-based malicious content stealthily or to evade security controls that rely on user interaction, posing a significant security risk. Relevant MITRE ATT&CK tactics: TA0005 Relevant MITRE ATT&CK techniques: T1497, T1562, T1204
name: Windows Chromium process Launched with Disable Popup Blocking id: 95f8acd6-978e-42d6-99c1-85baacdd2b46 version: 1 date: '2026-01-23' author: Teoderick Contreras, Splunk status: production type: Anomaly description: The following analytic detects instances where a Windows Chromium-based browser process is launched with the `--disable-popup-blocking` flag. This flag is typically used to bypass the browser’s built-in pop-up protections, allowing automatic execution of pop-ups or redirects without user interaction. While legitimate in some testing or automation scenarios, its presence on endpoints, particularly when combined with other automation or concealment flags, may indicate attempts by malicious actors to execute web-based content stealthily or evade user interaction controls, representing a potential security risk that warrants investigation. data_source: - Sysmon EventID 1 - Windows Event Log Security 4688 - CrowdStrike ProcessRollup2 search: | | tstats `security_co...endpoint-security malicious-activity TA0005 T1497 T1562 T1204 Apache License 2.0
This analytic detects instances where a Chromium-based browser process, including Chrome, Edge, Brave, Opera, or Vivaldi, is launched with an unusually small window size, typically less than 100 pixels in width or height. Such configurations render the browser effectively invisible to the user and are uncommon in normal user activity. This behavior may indicate attempts to execute web content or automated actions stealthily, bypassing user interaction and security controls, and can be a sign of malicious automation or covert browser-based activity. Relevant MITRE ATT&CK tactics: TA0005 Relevant MITRE ATT&CK techniques: T1497, T1564
name: Windows Chromium Browser Launched with Small Window Size id: 88103f56-8f5c-411f-a87f-71bee776f140 version: 1 date: '2026-01-23' author: Teoderick Contreras, Splunk status: production type: TTP description: The following analytic detects instances where a Chromium-based browser process, including Chrome, Edge, Brave, Opera, or Vivaldi, is launched with an unusually small window size, typically less than 100 pixels in width or height. Such configurations render the browser effectively invisible to the user and are uncommon in normal user activity. When observed on endpoints, especially in combination with automation, off-screen positioning, or suppression flags, this behavior may indicate attempts to execute web content or automated actions stealthily, bypassing user interaction and security controls. This analytic highlights potential malicious automation or covert browser-based activity. data_source: - Sysmon EventID 1 - Windows Event Log Security 4688 - CrowdStrike Process...defense-evasion execution endpoint-security TA0005 T1497 T1564 Apache License 2.0
This detection rule identifies an authentication bypass attempt in telnet, tracked as CVE-2026-24061. An attacker can exploit this vulnerability by providing a crafted USER environment variable, specifically `-f root`, which is passed to `/usr/bin/login`. The rule detects when the `telnetd` process spawns a `login` process with command-line arguments containing both `-p` and `-f root`, indicating an attempt to bypass authentication and gain root access without proper sanitization of user input. Relevant MITRE ATT&CK tactics: TA0004 Relevant MITRE ATT&CK techniques: T1548
name: Linux Telnet Authentication Bypass id: 6e0913d4-5461-487c-9dce-6d22ef2c0f03 version: 1 date: '2026-01-29' author: Raven Tait, Splunk status: production type: TTP description: Detects an authentication bypass in telnet tracked as CVE-2026-24061. An attacker can supply a specifically crafted USER environment variable (-f root) that is passed to /usr/bin/login. Because this input isn't sanitized an attacker can force the system to skip authentication and login directly as root. data_source: - Sysmon for Linux EventID 1 search: '| tstats `security_content_summariesonly` count min(_time) as firstTime max(_time) as lastTime from datamodel=Endpoint.Processes where Processes.process_name = "login" Processes.parent_process_name = "telnetd" Processes.process = "* -p *" Processes.process = "* -f root*" by Processes.action Processes.dest Processes.original_file_name Processes.parent_process Processes.parent_process_exec Processes.parent_process_guid Processes.parent_proce...privilege-escalation malicious-activity endpoint-security TA0004 T1548 CVE-2026-24061 Apache License 2.0
Detects callback scams originating from the legitimate WeTransfer noreply address. The rule uses natural language processing (NLP) to analyze the message body for high-confidence indicators of callback scam intent. This targets social engineering attacks that abuse trusted services to appear legitimate. Relevant MITRE ATT&CK tactics: TA0001 Relevant MITRE ATT&CK techniques: T1566
name: "Service abuse: WeTransfer callback scam" description: "Detects callback scams originating from legitimate WeTransfer noreply address using natural language processing to identify high-confidence callback scam intent in the message body." type: "rule" severity: "medium" source: | type.inbound and sender.email.email == '[email protected]' and any(ml.nlu_classifier(body.current_thread.text).intents, .name == "callback_scam" ) attack_types: - "Callback Phishing" tactics_and_techniques: - "Social engineering" - "Out of band pivot" detection_methods: - "Content analysis" - "Natural Language Understanding" - "Sender analysis" id: "c60c8650-e76e-501b-acf8-1feeb0e45bf2"