Description:
Premium feed that expands "Detection Rules Pro" Feed with analysis and guidance. The feed includes rule change analysis with impact guidance, correlation to active CVEs and threat campaigns, and a weekly detection engineering brief, all designed to support strategic decision-making, prioritization of efforts, and a robust, proactive detection posture. The feed is best suited for mature security operations centers, threat intelligence teams, and proactive detection engineers requiring advanced context.
Use cases:
- Risk-based prioritization - focus your team's efforts on deploying and tuning detections that address the most current and impactful threats.
- Improved situational awareness - gain a deeper understanding of how community detections align with the evolving threat landscape, active vulnerabilities, and adversary TTPs.
- Proactive detection posture management - move beyond reactive alerting to strategically curating and maintaining your detection capabilities based on actionable intelligence.
- Reduced fatigue and improved resource allocation - maximize the impact of your detection engineering by providing decision support with tactical and strategic intelligence about threat detection landscape.
Rules:
anvilogic: 75elastic-edr: 740elastic-siem: 1023fibratus: 83kql: 224osquery: 100sentinel: 4sigma: 1766splunk: 1976sublime: 3sublime-security: 444wazuh: 1yara: 462
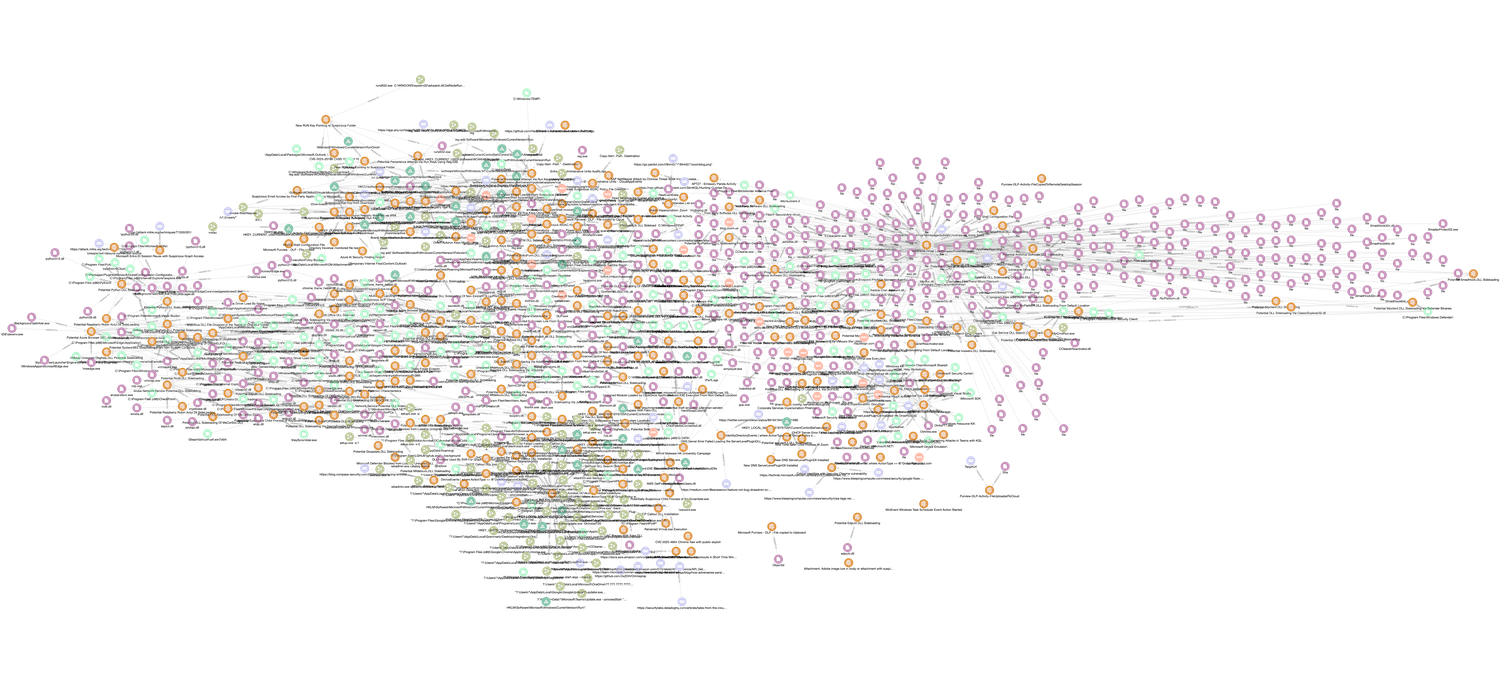
Entities:
Identity: 52 Indicator: 13387 Note: 11382 Report: 30 Directory: 6509Domain-Name: 2175Email-Addr: 42File: 11237Ipv4-Addr: 145Ipv6-Addr: 66Process: 11779Relationship: 63671Windows-Registry-Key: 1360
MISP feed:
STIX/TAXII feed:
Content preview:
Latest 10 entities:
This rule detects suspicious processes, such as cmd.exe or powershell.exe, making DNS queries to known abused web services like Pastebin, Discord, and Telegram. It utilizes Sysmon EventID 22 (DNS Query) and also checks if the process image path is located in common suspicious directories like Temp or AppData. This behavior is a strong indicator of an attempt to download a malicious payload or communicate with command-and-control infrastructure. Relevant MITRE ATT&CK tactics: TA0002, TA0011 Relevant MITRE ATT&CK techniques: T1059.005, T1105, T1071.001
name: Suspicious Process DNS Query Known Abuse Web Services id: 3cf0dc36-484d-11ec-a6bc-acde48001122 version: 14 date: '2025-12-10' author: Teoderick Contreras, Splunk status: production type: TTP description: The following analytic detects a suspicious process making DNS queries to known, abused text-paste web services, VoIP, instant messaging, and digital distribution platforms. It leverages Sysmon EventID 22 logs to identify queries from processes like cmd.exe, powershell.exe, and others. This activity is significant as it may indicate an attempt to download malicious files, a common initial access technique. If confirmed malicious, this could lead to unauthorized code execution, data exfiltration, or further compromise of the target host. data_source: - Sysmon EventID 22 search: '`sysmon` EventCode=22 QueryName IN ("*pastebin*", "*discord*", "*api.telegram*","*t.me*") process_name IN ("cmd.exe", "*powershell*", "pwsh.exe", "wscript.exe","cscript.exe") OR Image IN ("...malicious-activity command-and-control execution endpoint-security TA0002 TA0011 T1059.005 T1105 T1071.001 Apache License 2.0
[Impact: low][Scope: metadata] Update to "Suspicious Process DNS Query Known Abuse Web Services" rule
The rule's metadata was updated to associate it with two additional analytic stories, 'Braodo Stealer' and 'RedLine Stealer', enhancing its contextual mapping to known threats. The rule version and date were also revised. The core detection logic remains unchanged.
This detection rule identifies the creation of an executable (.exe), a configuration file (.exe.config), and a dynamic-link library (.dll) within the same directory. This pattern is characteristic of AppDomain Manager hijacking, a technique where an adversary loads a malicious assembly into a legitimate application's domain. The rule specifically monitors for these file creation events (Sysmon EventID 11) in common temporary or public folders to detect attempts at executing code under the guise of a trusted process. Relevant MITRE ATT&CK tactics: TA0003, TA0005 Relevant MITRE ATT&CK techniques: T1574.014
name: Windows Potential AppDomainManager Hijack Artifacts Creation id: be19b369-fd0c-42be-ae97-c10b6c01638f version: 1 date: '2025-12-10' author: Teoderick Contreras, Splunk status: production type: Anomaly description: The following analytic detects the creation of an .exe file along with its corresponding .exe.config and a .dll in the same directory, which is a common pattern indicative of potential AppDomain hijacking or CLR code injection attempts. This behavior may signal that a malicious actor is attempting to load a rogue assembly into a legitimate application's AppDomain, allowing code execution under the context of a trusted process. data_source: - Sysmon EventID 11 search: | | tstats `security_content_summariesonly` count min(_time) AS firstTime max(_time) AS lastTime from datamodel=Endpoint.Filesystem where Filesystem.file_name IN ("*.exe", "*.exe.config", "*.dll") AND Filesystem.file_path IN ("*\\windows\\fonts\\*", "*\\temp\\*", "*\\users\\public\\*", "*\\windows\\...defense-evasion persistence execution endpoint-security TA0003 TA0005 T1574.014 Apache License 2.0
This rule detects the creation of files within the Windows Startup folder, a directory commonly used by adversaries to establish persistence. By monitoring file system events in the specific path `...\Microsoft\Windows\Start Menu\Programs\Startup\`, the rule identifies when a new executable or script is placed to automatically run at user logon or system boot. A successful execution of this technique grants an adversary persistent access to the compromised system. Relevant MITRE ATT&CK tactics: TA0003, TA0002 Relevant MITRE ATT&CK techniques: T1547.001
name: Windows Boot or Logon Autostart Execution In Startup Folder id: 99d157cb-923f-4a00-aee9-1f385412146f version: 12 date: '2025-12-17' author: Teoderick Contreras, Splunk status: production type: Anomaly description: The following analytic detects the creation of files in the Windows %startup% folder, a common persistence technique. It leverages the Endpoint.Filesystem data model to identify file creation events in this specific directory. This activity is significant because adversaries often use the startup folder to ensure their malicious code executes automatically upon system boot or user logon. If confirmed malicious, this could allow attackers to maintain persistence on the host, potentially leading to further system compromise and unauthorized access to sensitive information. data_source: - Sysmon EventID 11 search: '|tstats `security_content_summariesonly` count min(_time) as firstTime max(_time) as lastTime from datamodel=Endpoint.Filesystem where File...persistence execution endpoint-security TA0003 TA0002 T1547.001 Apache License 2.0
[Impact: low][Scope: metadata] Update to "Windows Boot or Logon Autostart Execution In Startup Folder" rule
The rule's version and date have been updated. The `analytic_story` tag was expanded to include 'PromptFlux', linking the detection to an additional known threat. A key update was made to the Risk-Based Alerting (RBA) configuration by adding `file_name` as a tracked `threat_object`, which enhances the contextual information in generated risk events.
This Splunk rule detects DNS queries from endpoints to domains associated with AI platforms like Hugging Face and OpenAI. It leverages Sysmon Event ID 22 (DNS Query) to identify potential unauthorized use of external AI services or data exfiltration channels. The detection logic specifically excludes DNS queries originating from known browser processes to reduce false positives from legitimate user activity. Relevant MITRE ATT&CK tactics: TA0011, TA0010 Relevant MITRE ATT&CK techniques: T1071.004
name: Windows AI Platform DNS Query id: 1ad89d24-c856-4a0e-8fdf-c20c7b9febe1 version: 2 date: '2025-12-17' author: Teoderick Contreras, Splunk status: production type: Anomaly description: | The following analytic detects DNS queries initiated by the Windows AI Platform to domains associated with Hugging Face, OpenAI, and other popular providers of machine learning models and services. Monitoring these DNS requests is important because it can reveal when systems are accessing external AI platforms, which may indicate the use of third-party AI resources or the transfer of sensitive data outside the organization’s environment. Detecting such activity enables organizations to enforce data governance policies, prevent unapproved use of external AI services, and maintain visibility into potential data exfiltration risks. Proactive monitoring provides better control over AI model usage and helps safeguard organizational data flows. data_source: - Sysmon EventID 22 search: | `sysmon` E...command-and-control exfiltration endpoint-security TA0011 TA0010 T1071.004 Apache License 2.0
[Impact: medium][Scope: coverage] Update to "Windows AI Platform DNS Query" rule
The detection logic was updated to expand coverage by adding 'api.openai.com' to the list of monitored domains. The rule's accuracy was refined by removing a static list of process names and introducing a lookup-based exclusion for DNS queries originating from known browser processes. Metadata was also updated to include 'SesameOp' and 'PromptFlux' analytic stories and a new reference URL.
This rule detects processes executed from temporary directories, such as those matching '*\temp\*'. It analyzes EDR data from sources like Sysmon, Windows Security Events, or CrowdStrike to identify process creation events where the executable path is within a temp folder. Adversaries commonly use these locations to stage and run malicious payloads to bypass execution restrictions or avoid writing to more scrutinized directories, making this a key indicator of potential compromise. Relevant MITRE ATT&CK tactics: TA0003, TA0004, TA0005, TA0002 Relevant MITRE ATT&CK techniques: T1543, T1036.005, T1204.002, T1059
name: Windows Process Execution in Temp Dir id: f6fbe929-4187-4ba4-901e-8a34be838443 version: 7 date: '2025-12-10' author: Teoderick Contreras, Splunk status: production type: Anomaly description: The following analytic identifies processes running from %temp% directory file paths. It leverages data from Endpoint Detection and Response (EDR) agents, focusing on specific process paths within the Endpoint data model. This activity is significant because adversaries often use unconventional file paths to execute malicious code without requiring administrative privileges. If confirmed malicious, this behavior could indicate an attempt to bypass security controls, leading to unauthorized software execution, potential system compromise, and further malicious activities within the environment. data_source: - Sysmon EventID 1 - Windows Event Log Security 4688 - CrowdStrike ProcessRollup2 search: '| tstats `security_content_summariesonly` count min(_time) as firstTime ma...execution malicious-activity endpoint-security TA0003 TA0004 TA0005 TA0002 T1543 T1036.005 T1204.002 T1059 Apache License 2.0
[Impact: low][Scope: metadata] Update to "Windows Process Execution in Temp Dir" rule
The rule's version was incremented, the date was updated, and the 'SesameOp' malware family was added to the 'analytic_story' tags. This enhances the rule's contextual information by linking it to an additional known threat. The core detection logic was not modified.
This rule identifies processes executing from suspicious, non-standard file paths on Windows endpoints, such as Public, Fonts, Debug, or Recycle.bin directories. Adversaries use these locations to store and run malicious code to evade defenses and execute payloads without elevated privileges. The detection leverages EDR data, specifically monitoring process creation events originating from a list of unusual paths while excluding common temporary folder locations. Relevant MITRE ATT&CK tactics: TA0005, TA0002 Relevant MITRE ATT&CK techniques: T1543, T1036.005
name: Windows Suspicious Process File Path id: ecddae4e-3d4b-41e2-b3df-e46a88b38521 version: 18 date: '2025-12-10' author: Teoderick Contreras, Splunk status: production type: TTP description: The following analytic identifies processes running from file paths not typically associated with legitimate software. It leverages data from Endpoint Detection and Response (EDR) agents, focusing on specific process paths within the Endpoint data model. This activity is significant because adversaries often use unconventional file paths to execute malicious code without requiring administrative privileges. If confirmed malicious, this behavior could indicate an attempt to bypass security controls, leading to unauthorized software execution, potential system compromise, and further malicious activities within the environment. data_source: - Sysmon EventID 1 - Windows Event Log Security 4688 - CrowdStrike ProcessRollup2 search: '| tstats `security_content_summariesonly` coun...endpoint-security defense-evasion execution TA0005 TA0002 T1543 T1036.005 Apache License 2.0